Defense in depth (computing)
Defense in depth is a concept used in information security in which multiple layers of security controls (defense) are placed throughout an information technology (IT) system. Its intent is to provide redundancy in the event a security control fails or a vulnerability is exploited that can cover aspects of personnel, procedural, technical and physical security for the duration of the system's life cycle.
Background
The idea behind the defense in depth approach is to defend a system against any particular attack using several independent methods.[1] It is a layering tactic, conceived[2] by the National Security Agency (NSA) as a comprehensive approach to information and electronic security.[3][4] The term defense in depth in computing is inspired by a military strategy of the same name, but is quite different in concept. The military strategy revolves around having a weaker perimeter defense and intentionally yielding space to buy time, envelop, and ultimately counter-attack an opponent, whereas the information security strategy simply involves multiple layers of controls, but not intentionally ceding ground (cf. honeypot.)
Information security must protect information throughout its lifespan, from the initial creation of the information on through to the final disposal of the information.[5] The information must be protected while in motion and while at rest. During its lifetime, information may pass through many different information processing systems and through many different parts of information processing systems.[6] There are many different ways the information and information systems can be threatened. To fully protect the information during its lifetime, each component of the information processing system must have its own protection mechanisms.[7] The building up, layering on, and overlapping of security measures is called "defense in depth."[8] In contrast to a metal chain, which is famously only as strong as its weakest link, the defense in depth strategy aims at a structure where, should one defensive measure fail, other measures will continue to provide protection.[9]
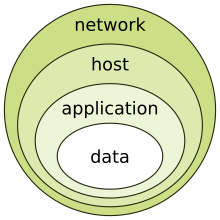
Recall the earlier discussion about administrative controls, logical controls, and physical controls. The three types of controls can be used to form the basis upon which to build a defense in depth strategy.[10] With this approach, defense in depth can be conceptualized as three distinct layers or planes laid one on top of the other.[11] Additional insight into defense in depth can be gained by thinking of it as forming the layers of an onion, with data at the core of the onion, people the next outer layer of the onion, and network security, host-based security, and application security forming the outermost layers of the onion.[12] Both perspectives are equally valid, and each provides valuable insight into the implementation of a good defense in depth strategy.[13]
Controls
Defense in depth can be divided into three areas: Physical, Technical, and Administrative.[14]
Physical
Physical controls[3] are anything that physically limits or prevents access to IT systems. Fences, guards, dogs, and CCTV systems and the like.
Technical
Technical controls are hardware or software whose purpose is to protect systems and resources. Examples of technical controls would be disk encryption, File integrity software, and authentication. Hardware technical controls differ from physical controls in that they prevent access to the contents of a system, but not the physical systems themselves.
Administrative
Administrative controls are organization's policies and procedures. Their purpose is to ensure that there is proper guidance available in regard to security and that regulations are met. They include things such as hiring practices, data handling procedures, and security requirements.
Methods
Using more than one of the following layers constitutes an example of defense in depth.
System and application
- Antivirus software
- Authentication and password security
- Encryption
- Hashing passwords
- Logging and auditing
- Multi-factor authentication
- Vulnerability scanners
- Timed access control
- Internet Security Awareness Training
- Sandboxing
- Intrusion detection systems (IDS)
Network
- Firewalls (hardware or software)
- Demilitarized zones (DMZ)
- Virtual private network (VPN)
Physical
- Biometrics
- Data-centric security
- Physical security (e.g. deadbolt locks)
See also
References
- ^ Schneier on Security: Security in the Cloud
- ^ "Some principles of secure design. Designing Secure Systems module Autumn PDF Free Download". docplayer.net. Retrieved 2020-12-12.
- ^ a b Defense in Depth: A practical strategy for achieving Information Assurance in today’s highly networked environments.
- ^ OWASP CheatSheet: Defense in depth
- ^ "Residents Must Protect Their Private Information". JAMA. 279 (17): 1410B. 1998-05-06. doi:10.1001/jama.279.17.1410. ISSN 0098-7484.
- ^ "Group Wisdom Support Systems: Aggregating the Insights of Many Through Information Technology". Issues in Information Systems. 2008. doi:10.48009/2_iis_2008_343-350. ISSN 1529-7314.
- ^ "INTERDEPENDENCIES OF INFORMATION SYSTEMS", Lessons Learned: Critical Information Infrastructure Protection, IT Governance Publishing, pp. 34–37, 2018, doi:10.2307/j.ctt1xhr7hq.13, ISBN 978-1-84928-958-0, retrieved 2021-05-29
- ^ "Managing Network Security", Network Perimeter Security, Auerbach Publications, pp. 17–66, 2003-10-27, doi:10.1201/9780203508046-3, ISBN 978-0-429-21157-7, retrieved 2021-05-29
- ^ Kakareka, A. (2013). "Chapter 31: What is Vulnerability Assessment?". In Vacca, J.R. (ed.). Computer and Information Security Handbook (2nd ed.). Elsevier. pp. 541–552. ISBN 9780123946126.
- ^ "Administrative Controls", Occupational Ergonomics, CRC Press, pp. 443–666, 2003-03-26, doi:10.1201/9780203507933-6, ISBN 978-0-429-21155-3, retrieved 2021-05-29
- ^ Duke, P. A.; Howard, I. P. (2012-08-17). "Processing vertical size disparities in distinct depth planes". Journal of Vision. 12 (8): 10. doi:10.1167/12.8.10. ISSN 1534-7362. PMID 22904355.
- ^ "Security Onion Control Scripts". Applied Network Security Monitoring. Elsevier. 2014. pp. 451–456. doi:10.1016/b978-0-12-417208-1.09986-4. ISBN 978-0-12-417208-1. Retrieved 2021-05-29.
- ^ Saia, Sergio; Fragasso, Mariagiovanna; Vita, Pasquale De; Beleggia, Romina. "Metabolomics Provides Valuable Insight for the Study of Durum Wheat: A Review". Journal of Agricultural and Food Chemistry. doi:10.1021/acs.jafc.8b07097.s001. Retrieved 2021-05-29.
- ^ Stewart, James Michael; Chapple, Mike; Gibson, Darril (2015). CISSP (ISC)2 Certified Information Systems Security Professional Official Study Guide. John Wiley & Sons. ISBN 978-1-119-04271-6.
